Protect
Secure
Safeguard
Safeguard Your Business Against Cyber Threats
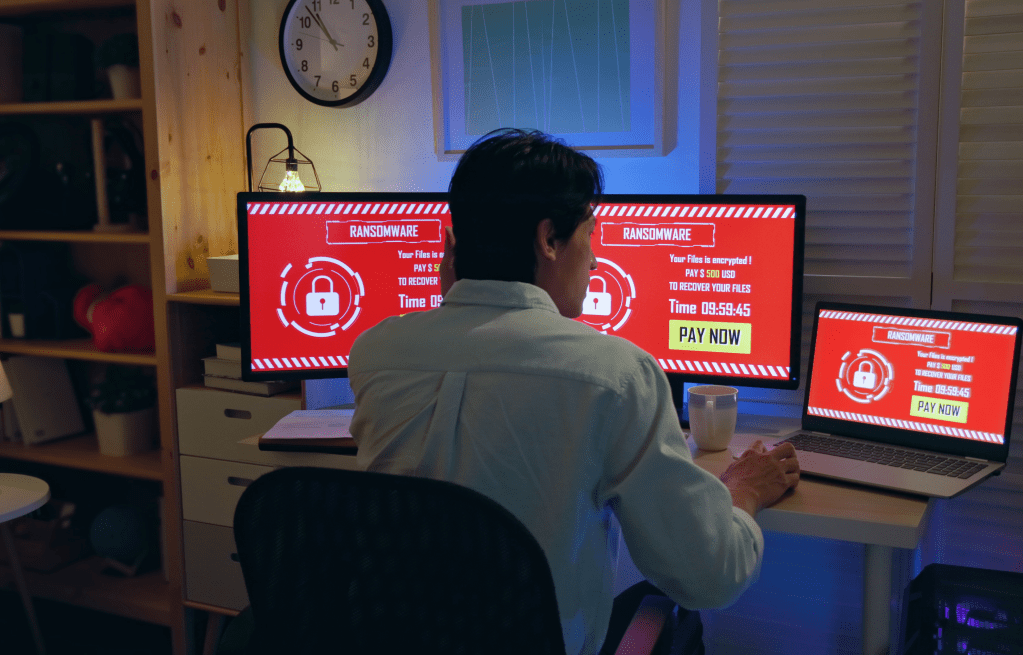
Cyber threats are more prevalent and sophisticated than ever before, and businesses confront an ever-expanding range of cyber threats. These threats can potentially compromise confidential data, interfere with daily operations, and harm brand credibility. It is imperative that you protect your company from these hazards and be proactive in knowing and guarding against cyber risks.
Important methods to defend your firm include implementing strong cybersecurity procedures, keeping up with the latest cyber threats, and regularly conducting cyber risk assessments. These tactics can reduce vulnerabilities and ensure your company is secure from cyberattacks and continues to run smoothly.

Benefits of GoodSuite Cyber Security
Iron-Clad Protection
Multi-layered, industry-leading security solutions to defend against hackers, malware, and cyber crime.
Continuous Monitoring
Around-the-clock surveillance to rapidly detect and respond to incidents before they escalate.
Compliance Assurance
Stay compliant with data security regulations for your industry (HIPAA, PCI, NIST, etc.)
Cost Savings
Avoid penalties, lost productivity, and recovery expenses from a cyber attack - a single breach can bankrupt some businesses.
GoodSuite: Your Trusted Partner for Cyber Risk Assessments
As you navigate the challenging world of cyber threats, GoodSuite is your reliable resource for keeping your business safe. Our highly trained team of cybersecurity experts is committed to assisting companies like yours in recognizing and efficiently reducing threats.
Our all-inclusive cyber risk assessment services aim to provide you with a detailed picture of your existing security status by identifying vulnerabilities and providing practical recommendations. Our use of cutting-edge technologies and techniques guarantees our comprehensive evaluation of your systems. To provide you with the most pertinent and recent guidance, our team of professionals keeps up to date on the most recent threats and industry best practices.
Still have questions? We have answers.
A Free Cyber Risk Assessment is a service offered by cybersecurity providers to evaluate your organization’s network and systems for vulnerabilities, threats, and security risks without any cost. It aims to identify potential security gaps and provide recommendations to improve your cybersecurity posture.
Considering a Free Cyber Risk Assessment helps you understand your current cybersecurity state, uncover hidden malware, and identify vulnerabilities within your network. It’s a proactive step towards enhancing your security measures and protecting your organization from potential cyber threats.
The assessment typically includes an evaluation of your network’s security vulnerabilities, detection of existing malware or threats, analysis of web and email traffic for risks, and an assessment of your data loss prevention strategies. The specifics can vary depending on the provider.
The duration of the assessment can vary based on the size and complexity of your network. Typically, it can range from a few days to a couple of weeks.
Preparation requirements can vary, but generally, you might need to provide access to your network and systems, ensure that relevant personnel are informed about the assessment, and possibly configure your systems to allow for the assessment activities.
After the assessment, the service provider typically delivers a comprehensive report detailing the findings, including identified vulnerabilities, potential threats, and recommendations for improving your cybersecurity defenses.
Reputable service providers ensure that your information remains confidential and secure during the assessment process. It’s important to discuss and understand their data protection and privacy policies beforehand.

